Taproot Critique Responses! Bitcoin Tech Talk Issue #175
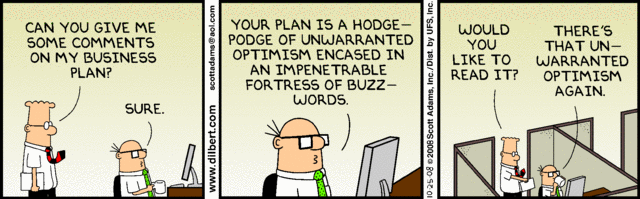
As I wrote last week, there were three different emails to the bitcoin-dev mailing list about the Taproot proposal. The writers are anonymous and I’ll be henceforth refer to them as the group. There have been several responses, and I’m going to attempt to summarize the arguments here. But first, a little background:
In Taproot, we have two paths that are hidden underneath a single output, a single key path (like p2pkh) and a script path (like p2sh). When spending to a Taproot output, there is no way to know which path will be used until it’s spent, adding privacy. Whenever the receiver wants only a single key to unlock the script, the script path requires a dummy. Whenever there’s just a script, users are encouraged to create an N-of-N single key which is enabled by Schnorr. The assumption being that if every possible signer agrees to move the funds, that doing so would be fine.
One of the questions from the group was of the N-of-N single-key path being useful or reasonable. Matt Corallo pointed out that prioritizing the N-of-N case to the protocol effectively incentivizes developers to prioritize its use and that incentivizing its use adds significant user privacy.
Another question from the group was whether doing MAST and Schnorr separately might be better than doing them together. David Harding argued that doing both at the same time was a privacy win and that the uses that Taproot/Schnorr optimize for (single key, N-of-N and K-of-N) cover the vast majority of how transactions are currently used on the network.
Anthony Towns wrote the most comprehensive response to the group’s questions. First, he argues that Taproot enables a free (in terms of block space) backup path to the single-key case and that this is a big win for user security. Second, he argues that Taproot is less expensive than MAST on-chain as the expected number of bytes required to reveal the what’s expected to be the most used Taproot path (single-key) is cheaper than the revealing a similar branch in the MAST tree. He backs this expectation up with statistics on how Bitcoin is used on chain. There are even better optimizations, as he mentions, but this may prevent future optimizations such as cross-input aggregations. He goes on to justify doing Schnorr and Taproot together because of the major wins in block space usage and utility.
Lastly, ZmnSCPxj pointed out that the parties themselves are going to be incentivized to use the N-of-N path as it’s cheaper fee-wise than using the script path.
Overall, I found the rebuttals pretty convincing and the major wins in privacy and block space are well thought out and should lead to better security practices going forward. Incidentally, reading through these technical arguments is good practice for contributing to Bitcoin Core, which I covered in my show last week.
Bitcoin
Ledger has published a bit of a self-serving post about secure elements and hardware in general. They break down the difference between a MCUs (micro-controller units) used in Trezor, safe memory chips used in ColdCard and secure elements used in Ledger, arguing that Ledger is the only one using a true secure element and thus the safest. Slush from Trezor has responded by pointing out that secure element vendors force NDAs which prevent disclosure of secure element hardware vulnerabilities. Also, there is no mention in Ledger’s blog post that their firmware is closed-source and thus harder to trust. This will likely come to a head at the Bitcoin 2020 conference when slush will explore this topic in a talk. I’m personally a fan of building your own hardware wallet from commodity components, but that’s still a bit of time away.
I read through BIP-320 this past week. If you’re curious about version bits and how some of them are now available for overt ASICBoost, this short video will give you insight.
Some interesting research suggests that orphan transactions incur a 17% overhead on network transmission. Orphan transactions are transactions where the parent is unknown and the default setting for Bitcoin Core is to keep a maximum of 100 such transactions around. The paper suggests that increasing the orphan transaction pool default to 1000 should mitigate the overhead.
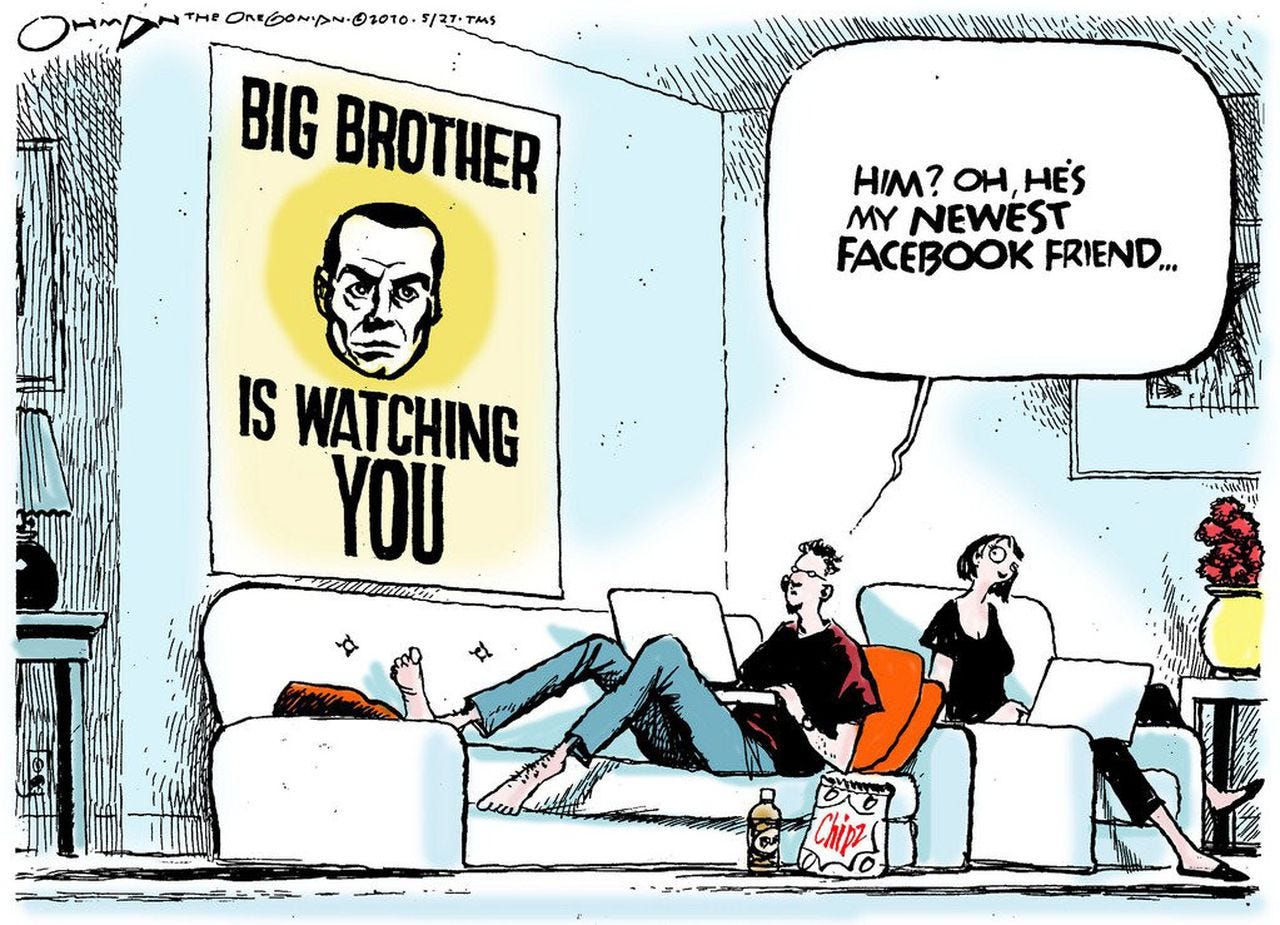
Alex Gladstein has written an essay on what the world in 2040 would look like with and without Bitcoin. He posits a future without Bitcoin being Orwellian with unprecedented surveillance using financial information. The future with Bitcoin is one that gives more power to the people. If you enjoyed Chapter 5 of The Little Bitcoin Book, this is essentially an expansion of that chapter. Definitely worth a read and worth thinking about.
In a scary precedent, a man faces 30 years in jail for providing a Bitcoin coinjoin mixing service. The service, Helix was popular among darknet merchants and customers to defeat attempts at chain analysis. He’s charged with transmitting money without a money transmitter license and conspiring to launder money. The scary part of this indictment is the implication that writing software could be considered a federal crime. Regardless, there will continue to be mixing services, they will simply operate in other countries.
Lightning
It looks like there’s some competition for Strike. Escher is a lightning app that also lets you pay lightning invoices using a debit card or bank account. As I mentioned previously, quick in-person payment using a debit card using lightning as a payment rail looks really powerful. I’m glad there are more companies that are coming to this realization.
A sobering research paper, whose authors include Christian Decker of Blockstream, suggests that the Lightning Network is becoming more centralized as it grows. The main conclusion is that the Lightning Network is becoming more centralized by many different metrics (how many nodes control how much of the capacity and so on). This is not a surprise as connected nodes will want to connect to other more connected nodes. I suspect that decentralization of the network and anonymity of transactions will require more services geared toward that end and user and developer prioritization of privacy. In addition, as some of these nodes go down for extended amounts of time, users will be taught to decentralize naturally. I spoke about this on Daily Brief with Tone Vays.
Economics, Engineering, Etc.
Phil Bonello has written an excellent long-read on the many ways in which Bitcoin is being adopted. He argues that there’s not just one reason driving Bitcoin’s adoption, but many, including digital gold, uncorrelated asset for a portfolio, as a protest to the current system and many others. Each reason has its own network effects causing even wider adoption, which is very bullish long-term. I had some similar thoughts in this interview I did back in December at laBitConf.
If you’re a fan of The Bitcoin Standard, Saifedean Ammous is pre-selling signed copies of his next book, Principles of Economics. This is an interesting experiment as fans will have access online to the book as it’s being written. I definitely recommend his ECO11 class and look forward to reading his new book.
Dragonfly Research has an excellent article on the economics of 51% attacks. Specifically, they go into how Bitcoin Gold was 51% attacked to double-spend against exchanges. Their main observation is that exchanges generally make enough money off of coins like Bitcoin Gold that they can afford double-spend losses like this. The bizarre phenomenon of coins going up after such attacks, however, is still a mystery.
Binance has published a nice introduction to Confidential Transactions. They go over how amounts are kept private using blinding factors and touch on the math involved.
Blockstack has stopped its developer incentive program: App Mining. The program was originally created to get developers to create apps on the Blockstack platform and distributed hundreds of thousands of dollars in BTC and STX tokens per month. It looks like the system got gamed with very basic apps on the platform getting the payouts. As this wasn’t really attracting new users, Blockstack decided to “pause” the program. This is what happens when you try to bribe your way to an ecosystem. It didn’t work for the Windows phone ecosystem and it doesn’t work for blockchain platforms. Ecosystems need real networks with real usage and a real reason to build. Every app on these blockchain platforms can be built much easier, faster and cheaper by using a SQL database instead.
Blockstack has also been criticized for unlocking another $6.8M in funding earlier this year by reaching their milestone of 1 million users. I’d be really surprised if they even had 10,000 real users on their platform, let alone 1 million. It turns out that the metric they used counted a “user” for every registration of a username, not any other activity. This is obviously an easily game-able metric and what I would call “decentralization theater.” I ranted about this on Tone’s Daily Brief this past week.
IOTA has a security vulnerability in their main wallet, Trinity, which has caused some users to lose funds. They’re spinning it as some sort of attack on their chain and they’ve stopped their chain completely. How? IOTA has a coordinator service which creates new blocks that the Iota Foundation unilaterally controls. They’ve turned off coordinator service, so all activity on Iota is paused. If you want to know why Bitcoin is fundamentally different than altcoins, this is a great example. Nobody has the power to “pause” Bitcoin.
Lastly, the coin Handshake airdropped tokens to Github users’ ssh keys. This is highly unusual and is meant to reward open source developers. If you have 15 or more followers on Github as of Feb 4, you can receive 4247 Handshake tokens by using your ssh key to sign a message. As this requires giving access to your private ssh key, it’s probably a good idea to rotate your ssh key on Github. The tokens as of this writing are worth $1000 or so. I don’t have a positive outlook on this project, but rotating ssh keys regularly is something you should do anyway. Getting paid for rotating keys is not a bad deal if you can convert to Bitcoin. Also, having dumped airdrops, I’ve found it’s better mentally to dump sooner than later. Note that for US users, you’ll have to register your name, phone number and birthday to get the funds out in BTC using namebase.io.
Las Vegas
I will be in Las Vegas this week for Unconfiscatable. I will be at the Carnivory Dinner and be on a couple of panels, but will not be at the Poker Tournament.
I’ll have some books with me or if you already have one, please bring it and I’ll sign it for you. The next event I’ll be at is in March at Bitcoin 2020 where I’ll also be having my seminar.
Fiat delenda est.